npm axios Supply Chain Attack (2026-03-31) — Check Versions 1.14.1 and 0.30.4 Right Now
On March 31, 2026, malicious axios versions 1.14.1 and 0.30.4 were published via a hijacked maintainer account. A plain-crypto-js postinstall hook deploys a cross-platform RAT. Microsoft and Google jointly attributed the campaign to North Korea's Sapphire Sleet / UNC1069.
목차 (12)
- Why Supply Chain Attacks Matter
- Attack Timeline — What Happened in 3 Hours
- Which Versions Are Dangerous
- How the Malicious Code Works
- Attack Vector — Maintainer Account Hijack
- How to Check Right Now
- Remediation
- Rotate Environment Variables and Credentials
- Prevention Routines
- Why This Keeps Happening
- FAQ
- Related
April 2026 · Security News
npm axios Supply Chain Attack (2026-03-31) — Check Versions 1.14.1 and 0.30.4 Right Now
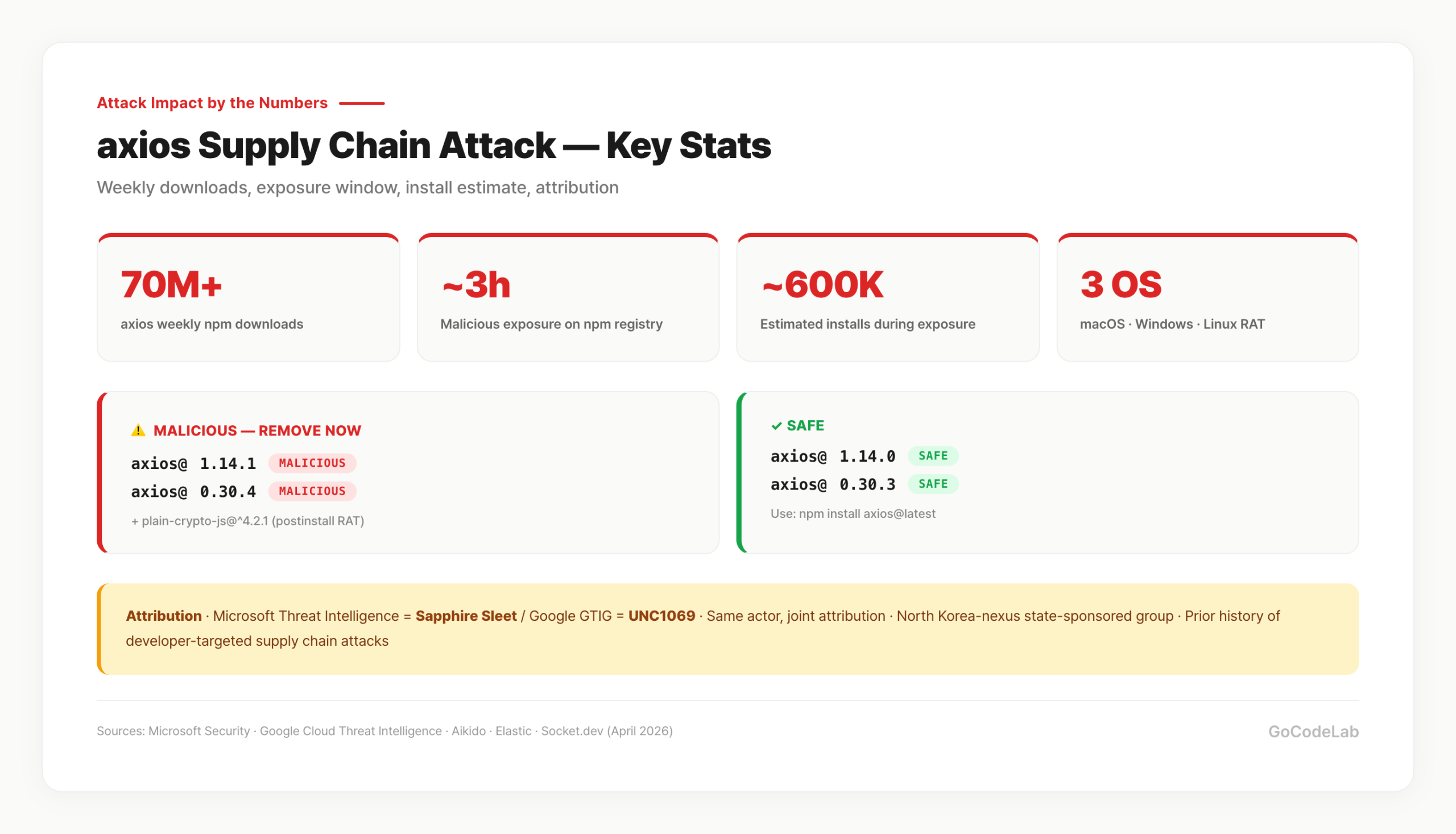
On March 31, 2026, malicious versions of npm axios — a package with 70M+ weekly downloads — were published after the maintainer's account was compromised via social engineering. Versions 1.14.1 and 0.30.4 were pushed back-to-back. Your code can be spotless; a poisoned dependency makes that irrelevant. Short version: check your version now.
The malicious releases sat on the npm registry for roughly 3 hours. In that window, an estimated 600,000 installs occurred, per analyses from Aikido Security and The Hacker News. Microsoft and Google jointly attributed the attack to the North Korea-nexus threat group Sapphire Sleet (tracked as UNC1069 by Google).
This article walks through how to check for compromise, how the malicious code works, and the step-by-step remediation. CI/CD pipelines must be reviewed too — not just local installs.
- Incident: March 31, 2026, 00:21 UTC (1.14.1) / 01:00 UTC (0.30.4)
- Malicious versions:
1.14.1, 0.30.4 (Safe: 1.14.0, 0.30.3)- Malicious dependency:
plain-crypto-js@^4.2.1 — postinstall hook drops RAT- Impact: ~3 hours live, estimated 600,000 installs
- Targets: macOS, Windows, Linux cross-platform
- Attribution: North Korea Sapphire Sleet (MS) / UNC1069 (Google) — joint attribution
- Action: upgrade to safe version + rotate all environment variables and credentials
Why Supply Chain Attacks Matter
A supply chain attack targets the distribution channel rather than your code. Like swapping the contents of a shipping box. The more popular the package, the more valuable the target. axios pulls 70M+ weekly downloads — a near-ideal target.
Compromise an npm account or abuse publishing permissions and a malicious version goes live quietly. Automated CI/CD pipelines pull the new version and spread it across countless projects. Damage accumulates before anyone notices. In this case, 600K installs happened in 3 hours.
"Popular packages are safe" is exactly the assumption attackers exploit. Higher trust, less scrutiny. axios is the de facto standard HTTP client across React, Vue, and Angular apps — that's why the blast radius is so wide.
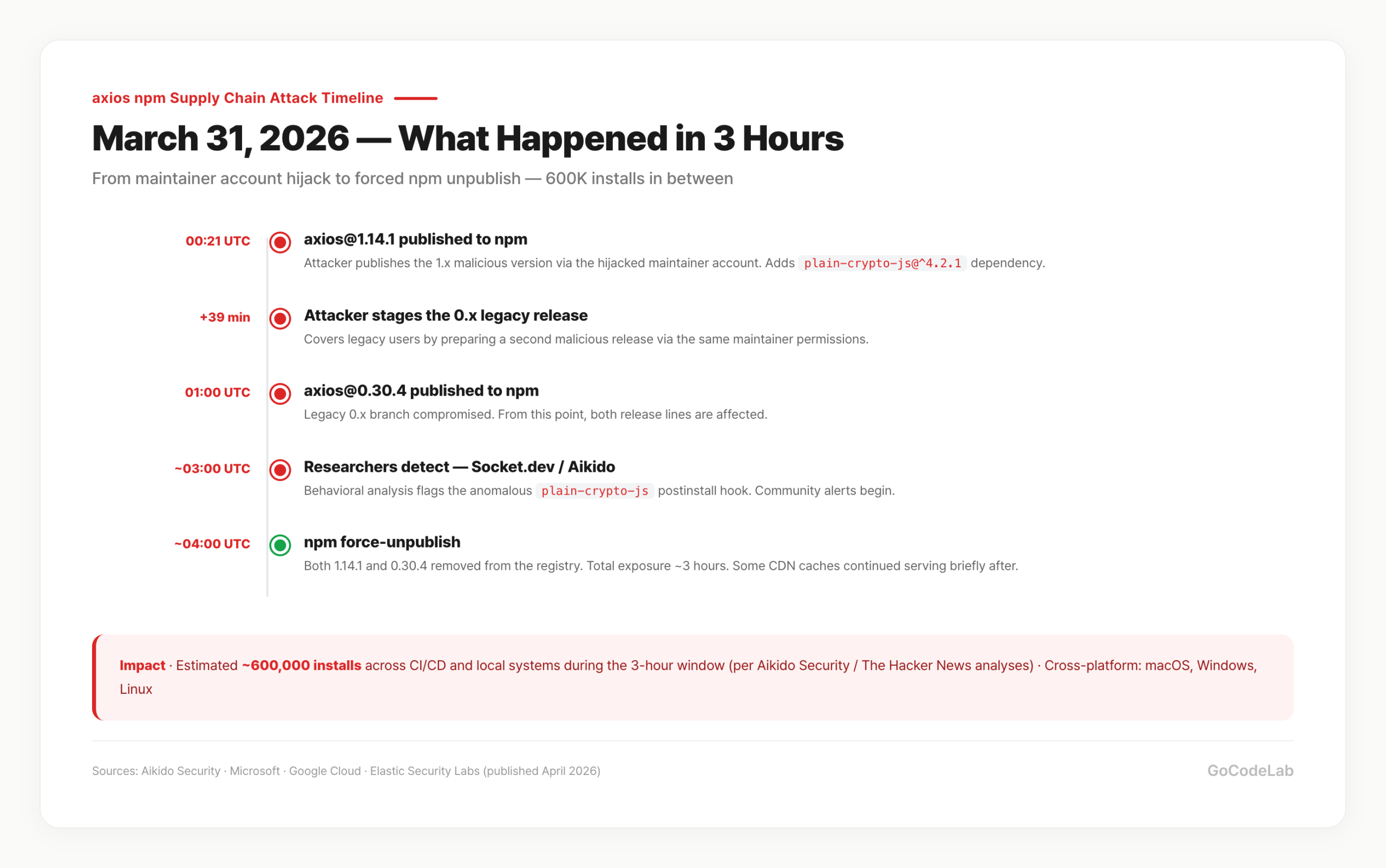
Attack Timeline — What Happened in 3 Hours
Independent reconstructions from Aikido Security, Arctic Wolf, and Elastic Security Labs largely agree on the timeline.
- 2026-03-31 00:21 UTC —
axios@1.14.1published to npm. Targets the 1.x line. - +39 minutes — Attacker queues up the legacy 0.x line release.
- 01:00 UTC —
axios@0.30.4published. Both 1.x and 0.x branches compromised in sequence. - ~03:00 UTC — Security researchers detect the unusual plain-crypto-js dependency. Socket.dev and Aikido alert.
- ~04:00 UTC — npm force-unpublishes both versions. Total exposure ≈ 3 hours.
- ~600,000 installs — Estimated total across CI/CD and local installs during the window.
"Only 3 hours" is a dangerous framing. Vercel, GitHub Actions, CircleCI, and similar CI environments pull fresh versions on cache misses every 10~30 seconds. Globally, tens of thousands of builds ran in that window. Several regions also reported CDN cache serving the malicious version briefly after the unpublish.
Which Versions Are Dangerous
The malicious versions are 1.14.1 and 0.30.4. They pull plain-crypto-js@^4.2.1 as a dependency, which executes a postinstall hook that deploys the RAT.
·
1.14.1 (malicious) / 1.14.0 (safe)·
0.30.4 (malicious) / 0.30.3 (safe)· Post-incident releases: 1.15.0+ and 0.30.5+ — safe (official post-mortem releases)
Legitimate axios releases do not contain plain-crypto-js. This package is never imported anywhere in axios source. It exists solely to execute its postinstall hook. Version numbers can look familiar — trust only the lock file.
Adjacent versions like 1.14.0 and 1.13.x are unaffected. But if you use range specifiers (~, ^) with auto-updates, you may have accidentally picked up the malicious version. Audit the version ranges in your package.json.
How the Malicious Code Works
plain-crypto-js disguises itself as a crypto utility. During install, npm runs its postinstall script automatically. That hook contacts the attacker's C2 (Command & Control) server and pulls a second-stage payload.
The payload detects the host OS and drops a matching RAT (Remote Access Trojan). Think of it as someone copying your house key and handing it to a third party — you lose persistent access control over the machine.
Targets are cross-platform: macOS, Linux, Windows. CI/CD runners, build containers, local dev machines — all vulnerable. Per Elastic Security Labs, the C2 protocol rides on HTTPS with a custom command set designed to blend into normal API traffic, making network-level detection difficult.
Once the RAT is in, it's not just environment variables — the attacker holds system-level access.
process.env is a given, but file systems, internal networks, SSH keys, and browser-stored credentials are all reachable in principle. AWS_ACCESS_KEY, OPENAI_API_KEY, DATABASE_URL, NEXTAUTH_SECRET, STRIPE_SECRET_KEY — whatever is injected at build time is on the exfiltration list.
Attack Vector — Maintainer Account Hijack
Per SANS Institute and The Hacker News, the axios maintainer account was hijacked through a targeted social engineering campaign. The attacker changed the account email to ifstap@proton.me, then abused publish permissions to push the two releases in sequence.
UNC1069 / Sapphire Sleet has a track record of targeting developers via supply-chain routes. Three common patterns: first, fake job offers with malicious coding-test files; second, fake recruiter outreach via LinkedIn or Telegram; third, phishing open-source maintainers directly. This axios case appears to fall into the third pattern.
Being a state-sponsored actor changes the motivation and resources calculus. This isn't a script kiddie incident — the campaign is designed for stealth and persistence, with one poisoned package reaching tens of thousands of projects simultaneously.
How to Check Right Now
Two lines are enough. Run these in your terminal.
npm list axios
# Check for malicious versions in lock file
grep -E "axios@(1\.14\.1|0\.30\.4)|plain-crypto-js" package-lock.json
# Monorepo-wide scan
find . -name "package-lock.json" -not -path "*/node_modules/*" | xargs grep -l "plain-crypto-js\|1.14.1\|0.30.4"
If grep returns a match, remediate immediately. No output means you're probably fine — but also check git history. If the malicious version was ever installed in the past, the postinstall hook has already run.
git log -p -- package-lock.json | grep -E "1\.14\.1|0\.30\.4|plain-crypto-js"
With pnpm, use pnpm list axios; with yarn, yarn list --pattern axios. The lock-file grep pattern applies regardless of package manager.
Remediation
Upgrade to the latest safe version and rebuild the lock file.
rm -rf node_modules package-lock.json
# 2. Install the latest safe version
npm install axios@latest
# 3. Verify
grep "plain-crypto-js" package-lock.json
# → No output = clean
Completely wiping node_modules and reinstalling is the safest path — caches can still serve stale entries. Run npm cache clean --force too. Apply the same to deployment environments (Vercel / Netlify / GitHub Actions caches).
Rotate Environment Variables and Credentials
If a malicious version ever reached your machines, the RAT may still be resident. Don't rotate just environment variables — treat the whole credential surface as compromised.
□ AWS / GCP / Azure access keys
□ AI API keys — OpenAI / Anthropic / Gemini
□ Database passwords — PostgreSQL, MySQL, MongoDB
□ Payment API keys — Stripe, LemonSqueezy, Paddle
□ GitHub Personal Access Token + SSH keys
□ App secrets — NEXTAUTH_SECRET, SESSION_SECRET
□ Webhook secrets for external services
□ Infected-machine SSH public keys — remove entries from
~/.ssh/authorized_keys on any servers they were copied to
Revoke old keys immediately after issuing new ones. Keeping the old key alive defeats the rotation. Follow each provider's dashboard for the proper revocation flow.
For machines with high suspicion of compromise, an OS reinstall is the safest option. CI runner images should be rebuilt clean. Local dev machines should at minimum clear browser sessions, SSH keys, and saved AWS CLI profiles, then reconfigure.
Prevention Routines
Commit lock files to git — always. Lock files pin the exact installed versions. If they're in .gitignore, remove that now. Without a lock file, every build can pull a different version.
Put npm audit in your CI pipeline. Run it on every PR. npm audit --audit-level=high catches high-severity issues at minimum. Caveat: audit only sees what's public in the CVE database.
Tighten version range specifiers in package.json. ^1.13.0 quietly opens the door to minor-version auto-updates — including malicious ones. Pin exact versions (1.14.0) or narrow to patch-only (~1.14.0) for critical packages.
· Dependabot — GitHub built-in. Auto-opens PRs on vulnerability discovery. CVE-based.
· Socket.dev — Supply-chain specialist. Behavioral analysis detects novel attacks. Flagged this axios incident early.
· Snyk — Vulnerability scanning + remediation. Free tier available.
· Aikido Security — Published the first public analysis of this incident. Strong real-time behavioral analysis.
· npm audit — Built-in. CVE-based, so limited against fresh attacks.
Realistic combo: Dependabot + Socket.dev. Single-tool reliance leaves blind spots.
Why This Keeps Happening
The npm ecosystem has a low publishing bar. A single account compromise can poison a package used by hundreds of millions of developers. That structural fact isn't changing fast.
XZ Utils (2024-03), event-stream (2018), ua-parser-js (2021), and now axios (2026-03) — high-profile supply chain attacks keep landing. axios isn't the first and won't be the last. If you use open source, this risk is structural.
Following this incident, npm is reportedly considering mandatory 2FA expansion and a 24-hour cooldown on maintainer email changes. GitHub already required 2FA for top npm maintainers since 2024, but this hijack went through the email recovery flow. Security chains only hold as strong as the weakest link.
Regular audits and automated monitoring are the realistic defense. Perfect defense doesn't exist. Fast detection and quick response routines are what actually work. Use this incident to revisit your dependency management practices.
FAQ
Q. When did the attack happen?
axios@1.14.1 was published at 00:21 UTC on March 31, 2026, followed by axios@0.30.4 at 01:00 UTC. The malicious versions were live for about 3 hours; an estimated 600,000 installs occurred during the window.
Q. What are the safe versions?
The clean releases preceding the attack were 1.14.0 and 0.30.3. Post-incident clean releases by the axios team (1.15.0+, 0.30.5+) are also safe. npm install axios@latest upgrades you to a safe release.
Q. Can npm audit catch everything?
Not initially. npm audit runs against the public CVE database. Fresh supply chain attacks pass through until a CVE is registered. Behavior-analysis tools like Socket.dev or Aikido are needed as complements.
Q. Does this affect yarn and pnpm too?
Package manager is irrelevant — the registry is the same. Check lock files with the appropriate command: yarn.lock for yarn, pnpm-lock.yaml for pnpm.
Q. Who did it?
Microsoft Threat Intelligence tracks the actor as Sapphire Sleet; Google's GTIG tracks the same actor as UNC1069. Both companies confirmed the joint attribution to North Korea. The group's primary motive is financial — cryptocurrency-related organizations are frequent targets — but this campaign targeted general-purpose developers at scale.
Q. How do I check in a monorepo?
Check every workspace's lock file, not just the root. find . -name "package-lock.json" -not -path "*/node_modules/*" | xargs grep "plain-crypto-js" scans the whole repo quickly.
This incident is a good moment to revisit dependency management. Lock files committed, regular audits, real-time monitoring — those three alone catch most supply chain attacks early.
Trusting a popular package and verifying it are different things. If you use axios, put a version check in your routine starting today.
· axios Official Post-Mortem (GitHub #10636)
· Microsoft Security Blog — Mitigating the Axios npm supply chain compromise
· Google Cloud Threat Intelligence — UNC1069 analysis
· Aikido Security — first public analysis
· Elastic Security Labs — RAT technical analysis
· Socket.dev — plain-crypto-js analysis
· Snyk Security Blog
This article is based on analyses published as of April 2026 by Microsoft, Google, Aikido, Elastic, Socket.dev, SANS, and The Hacker News. Situations may evolve; verify against official channels.
Security vulnerability information can change based on disclosure timelines. GoCodeLab is not responsible for outcomes resulting from direct application of the content in this article.